July 17, 2020 / Nirav Shah
This blog is very useful for software developers and server administrators to save their time and improve work productivity for the company.
If you’re a developer/ server admin you might be facing some issue during this pandemic situation.
Well let’s talk about the actual issue:
While we went to the office most of the companies have set a static IP address for every single person. But nowadays as we know most of the companies have given permission to work from home to their employees. So in this scenario, the broadband IP addresses are always dynamic so every time developer has to text the administrator to add their IP address in the AWS security group.
This is comparatively an easy task for a server administrator to do. But what if something happens and the administrator is not able to add the IP address on the security group.
So waiting for administrator……….? No way.
Now here comes the solution, by our AWS expert team for the developer so that anyone can add his/her IP address on the AWS security group.
Step 1
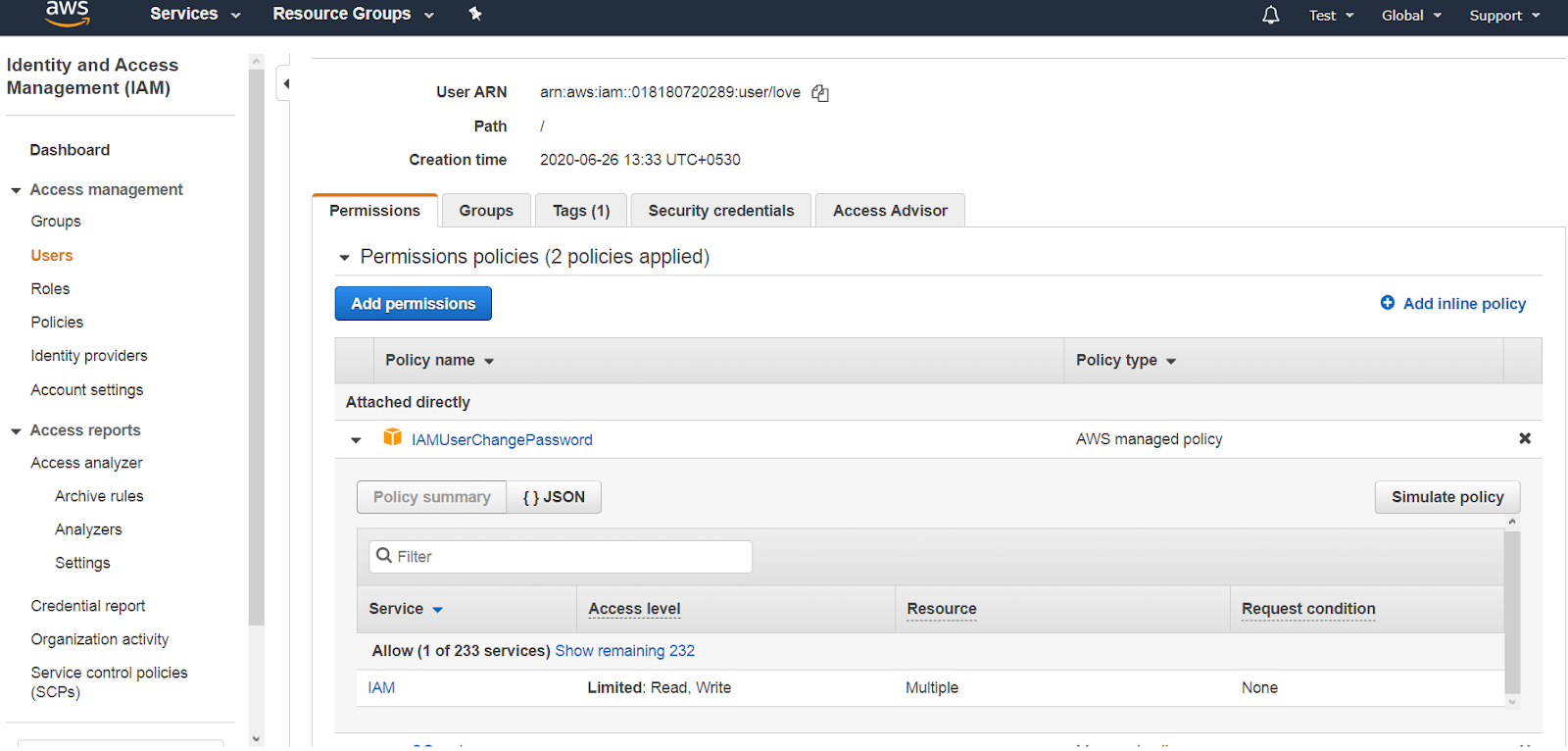
Create an IAM user
Step 2
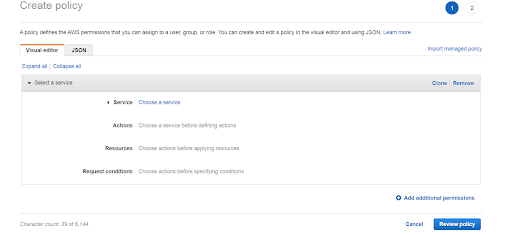
Create a custom JSON policy as given below
{
"Version": "2012-10-17",
"Statement": [
{
"Effect": "Allow",
"Action": [
"ec2:AuthorizeSecurityGroupEgress",
"ec2:AuthorizeSecurityGroupIngress",
"ec2:RevokeSecurityGroupEgress",
"ec2:RevokeSecurityGroupIngress"
],
"Resource": "arn:aws:ec2:*:*:security-group/*",
"Condition": {
"ArnEquals": {
"ec2:Vpc": "arn:aws:ec2:*:*:vpc/vpc-vpc-id"
}
}
},
{
"Action": [
"ec2:DescribeSecurityGroups",
"ec2:DescribeSecurityGroupReferences",
"ec2:DescribeStaleSecurityGroups",
"ec2:DescribeVpcs"
],
"Effect": "Allow",
"Resource": "*"
}
]
}
In place of text “vpc-vpc-id” you have to add your VPC id.
You can also specify like, which security group will be accessible.
Suppose here we can add only our IP on “sg-0735b94567cdbde36” security group.
Example of our demo script:
{
"Version": "2012-10-17",
"Statement": [
{
"Effect": "Allow",
"Action": [
"ec2:AuthorizeSecurityGroupEgress",
"ec2:AuthorizeSecurityGroupIngress",
"ec2:RevokeSecurityGroupEgress",
"ec2:RevokeSecurityGroupIngress"
],
"Resource":"arn:aws:ec2:*:018180720289:security-group/sg-0735b94567cdbde36",
"Condition": {
"ArnEquals": {
"ec2:Vpc": "arn:aws:ec2:*:*:vpc/vpc-5940bd33"
}
}
},
{
"Action": [
"ec2:DescribeSecurityGroups",
"ec2:DescribeSecurityGroupReferences",
"ec2:DescribeStaleSecurityGroups",
"ec2:DescribeVpcs"
],
"Effect": "Allow",
"Resource": "*"
}
]
}
Now, Let’s describe the custom policy.
This custom policy is only accessible for particular security groups in which only you can add an IP address on security groups and if someone tries to delete the existing security group it will show up the error message.
Like this,
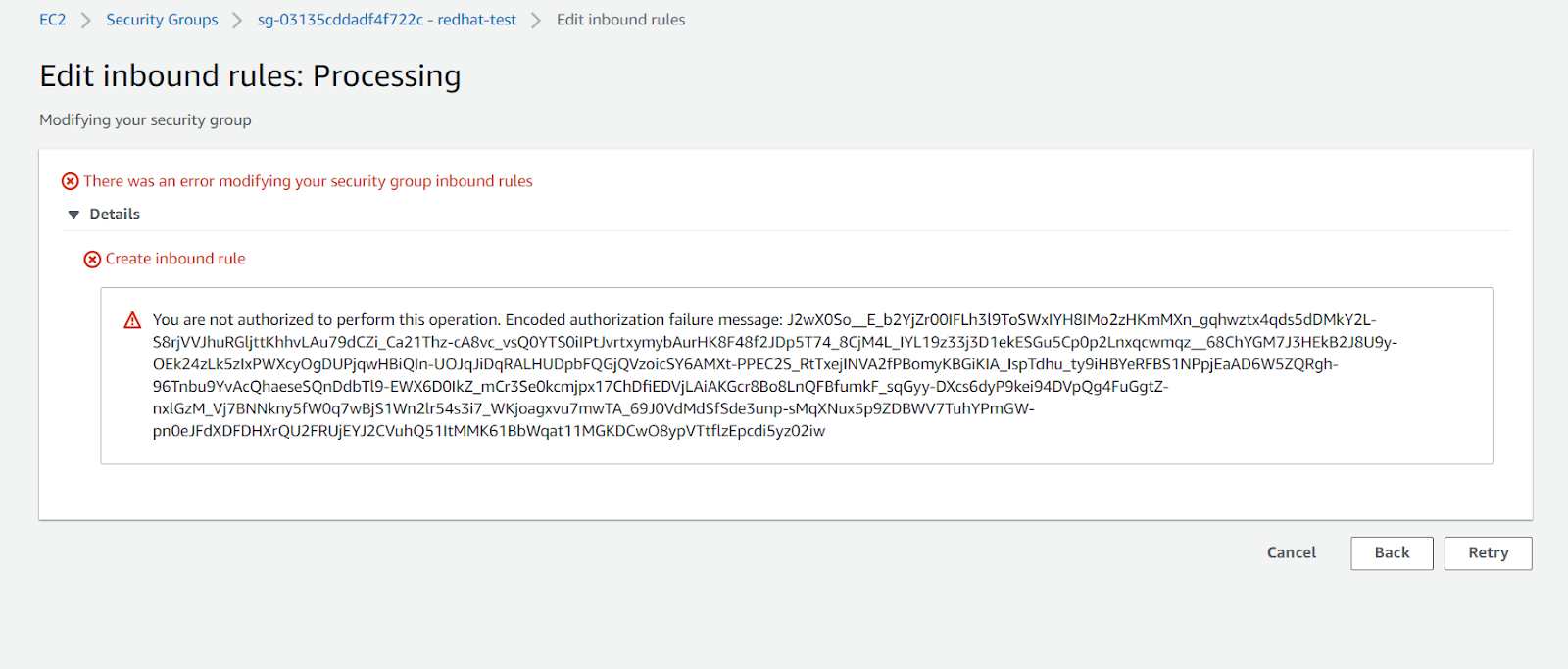
So it’s completely secure.
This policy is very useful and it can improve the productivity of the company and save the time of the developer as well as the administrator.
Also Read: AWS Security Hub
Services: AWS Security Management & Consulting Services

Nirav Shah is the Director of Eternal Web Pvt Ltd, an AWS Advanced Consulting Partner and certified Odoo Partner based in the UK. With over a decade of experience in cloud computing, digital transformation, and ERP implementation, Nirav helps enterprises adopt the right technology to solve complex business challenges. He specialises in AWS infrastructure, Odoo ERP, and web development solutions for businesses across the UK and beyond.
Have queries about your project idea or concept? Please drop in your project details to discuss with our AWS Global Cloud Infrastructure service specialists and consultants.