July 17, 2020 / Nirav Shah
Have you thought about what following points mean in AWS and cybersecurity in general?
If you are working as a security consultant that you must be aware of topics like these, but if not, don’t worry we will explain to you in details.
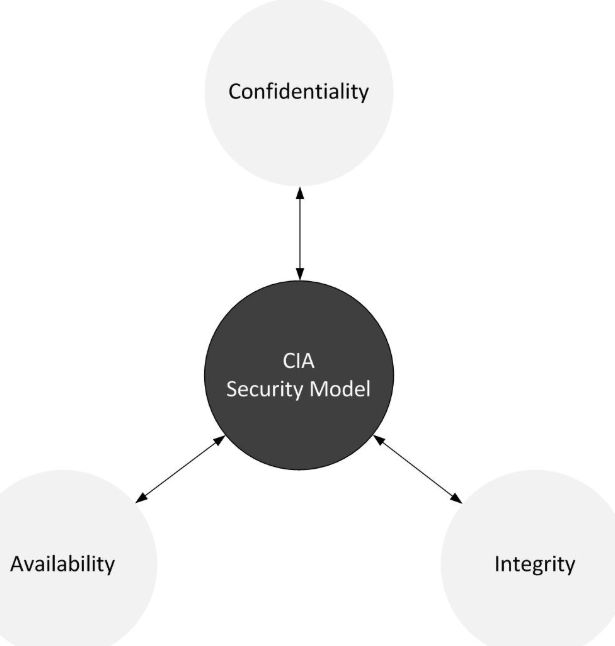
What is the CIA?
It is Confidentiality, Integrity and Availability. Sometimes these three points can be referred to as “The Triad”.
Good examples of confidentiality are things like using data encryption. So encrypting our data at rest, encrypting our data in transit, things like user IDs and passwords. Things like two-factor authentication, which we use in Identity Access Management on AWS. So confidentiality. Think of these as basic level privacy.
Integrity involves maintaining consistency, accuracy and trustworthiness of data over its entire life cycle.
Example
Checksum, when you download a piece of software, there will always be a Checksum next to it, and then you can essentially once you’ve downloaded it, you can check the hash of that software to the Checksum and if they match then you know that the data is correct.
And then Availability
Suppose you set up infrastructure on the cloud, what points are to be you kept in mind?
Example: You want redundancy over everything. So you want your disk to be rated,
you want high availability clusters, you want multiple availability zones, multiple regions,
and you want to design for failure as well so that you basically will have very high availability.
So now let’s see how AWS can help to the above model.
In confidentiality obviously you wanna keep your data confidential, so we would use things like Identity Access Management, and Multi-Factor Authentication. It might also use things like Bucket Policies, we might use things like security groups, or access control lists within our VPC. That is all about Confidentiality.
In Availability simple and short.
Integrity
AWS has their own SSL service now, so they’ve got Certificate Managers. So keeping your data with good integrity. And also things like inside S3. So things like Version Control, Multi-Factor Authentication when you’re trying to delete things inside S3, you can require that somebody provides an MFA token before that object is deleted.
You must read this blog “AWS shared responsibility” For more information visit Here.

Nirav Shah is the Director of Eternal Web Pvt Ltd, an AWS Advanced Consulting Partner and certified Odoo Partner based in the UK. With over a decade of experience in cloud computing, digital transformation, and ERP implementation, Nirav helps enterprises adopt the right technology to solve complex business challenges. He specialises in AWS infrastructure, Odoo ERP, and web development solutions for businesses across the UK and beyond.
Have queries about your project idea or concept? Please drop in your project details to discuss with our AWS Global Cloud Infrastructure service specialists and consultants.